Products / Quest / KACE Desktop Authority

Use KACE Desktop Authority to eliminate the hassle of deploying and securing network-connected devices by customizing them at first login. Easily configure firewall and browser security settings for physical, virtual and published Windows environments. Ensure that applications are maintained and access to network resources is always available.
Key Features
- Flexible criteria-based settings and configurations
- Windows environment management
- Remote user support
- Device security
Secure, privileged access to systems and data
Business stakeholders require greater flexibility in IT operations, but administrators must still maintain a secure and consistent user environment. They can no longer rely on the traditional model of managing only the machine. Each user needs to be granted the right access to the right resources regardless of the device used.
KACE Desktop Authority is the foundation for our centralized, secure desktop management software for Windows environments, KACE Desktop Authority Management Suite. Along with KACE Privilege Manager, you can maintain the balance between security and user productivity while saving IT resources.
Benefits
Customize Devices
Customize devices while configuring the firewall and controlling browser security for physical, virtual and published Windows environments.
Manage Applications
Make sure applications are always available and maintain access to network resources.
Maintain Identities
Shape user environments while instantly configuring drives, printers, folders, shortcuts, Outlook profiles, and more.
Empower Users
Let users customize their computers ? within the limits you specify and without giving them local admin rights.
We are the Desktop Authority reseller for Thailand.
For further information please contact with our sales department at:
Bangkok phone number +66 (2) 401 9255
e-mail: sales@nullnsasia.co.th or visit the Desktop management software for Windows (quest.com) website
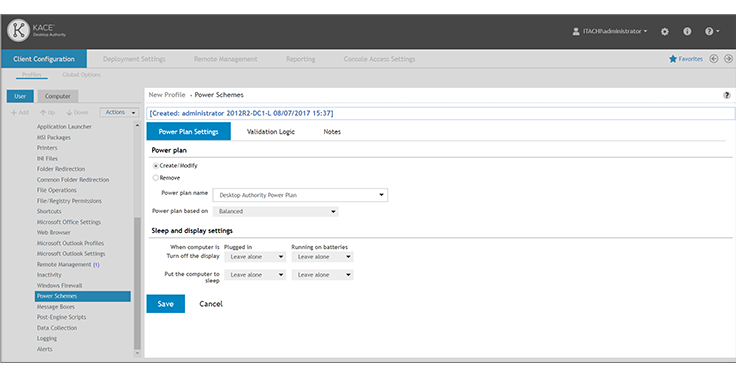
Proactively provision and manage Windows systems with Desktop Authority Management Suite. Comprised of Desktop Authority and Privilege Manager, the full suite secures endpoint devices, including USB ports, and runs your applications in a least-privileged environment and your data is protected. Centrally manage firewall settings, power consumption, and easily target and customize user configurations without logon scripts. Maintain the balance between security and user productivity while saving IT resources.
Features
Keep sensitive data within your organization and prevent vulnerabilities from being introduced by end users, without limiting capabilities or causing productivity issues for users.
Gather all privilege usage information into a central database and run domain-level analysis to easily determine if privilege policies need to be modified to meet compliance requirements.
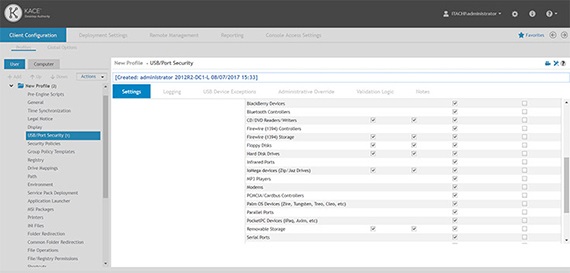
Control both device usage (like external drives, printers, cameras and mobile devices), as well as port access (such as serial, infrared, USB and more), according to each user’s unique authentication and access levels.
Remotely manage issues behind the scenes using more than 30 different management tasks without disrupting user productivity.
Keep your mobile users working, and your network secure. Validation Logic?s advanced targeting features ensure the correct elevation settings always apply when a user travels between offices.